Security Solutions
Protecting your business at every layer. Digital and physical.
Security isn't one product or one camera on the wall. It's a set of overlapping layers — your network, your endpoints, your email, your physical entrances, your server room, and the people who walk through your door every day. A gap in any one of these is a gap in all of them.
We've delivered security solutions for environments that demand high standards — including the Consulate General of the UAE's Hyderabad office, where there was no room for informal procedures or undocumented access. We bring the same disciplined, documented approach to every client we work with, whether you're a 20-person company in Kondapur or a multi-facility enterprise in Secunderabad.
We work across
IT security
Cybersecurity
CCTV
Biometric access control
Physical access control
all from one team, all under one contract if you need it. No separate vendors for physical and digital. No gaps between them.

IT & Network Security
Your network is either defended or it isn't. There's no in between.
Endpoint Protection · Network Hardening · Cisco · Aruba · Fortinet · Sophos
What IT & Network Security covers:
Firewall setup, EDR, hardening, and ongoing management — Fortinet, Sophos, Cisco, Palo Alto
Intrusion detection and prevention system (IDS/IPS) configuration
Wi-Fi security — WPA3, certificate-based authentication, rogue AP detection
Zero Trust Network Access (ZTNA) for remote workers
Network access control (NAC) — only authorised devices connect
Security event log monitoring and alerting (SIEM lite)
Network security documentation and policy creation
Brands we deploy and manage: Cisco (ASA, Meraki, Catalyst), Aruba (switches, wireless, ClearPass NAC), Fortinet FortiGate, Sophos XG/XGS. For endpoint security: CrowdStrike, SentinelOne, Microsoft Defender for Business.


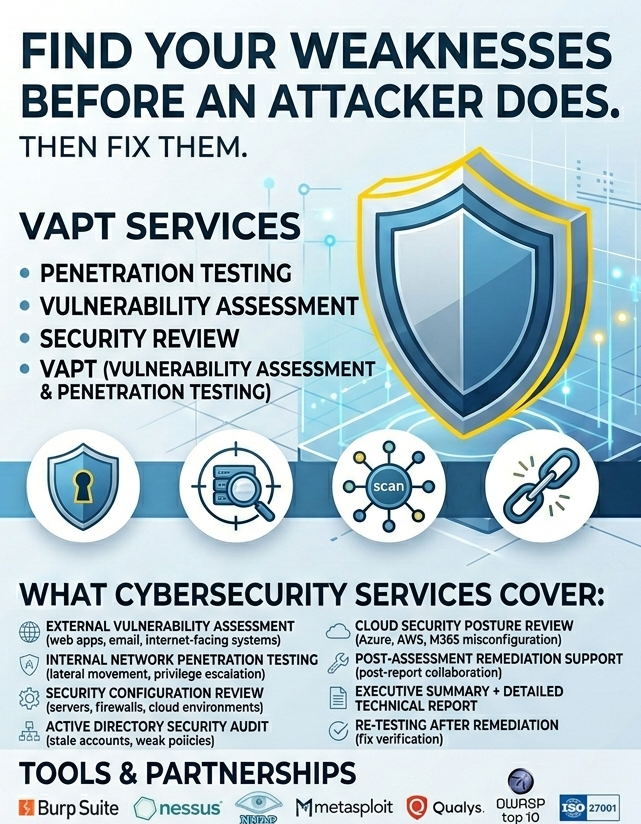
Find your weaknesses before an attacker does. Then fix them.
Penetration Testing · Vulnerability Assessment · Security Review · VAPT
What cybersecurity services cover:
External vulnerability assessment — internet-facing systems, web apps, email infrastructure
Internal network penetration testing — lateral movement, privilege escalation paths
Security configuration review — servers, firewalls, cloud environments
Active Directory security audit — stale accounts, weak policies, privilege escalation risks
Cloud security posture review — Azure, AWS, and Microsoft 365 misconfiguration audit
Post-assessment remediation support — we don't hand you a report and disappear
Executive summary for management + detailed technical report for IT
Re-testing after remediation to verify fixes are effective
Cybersecurity (Assessments & Penetration Testing)
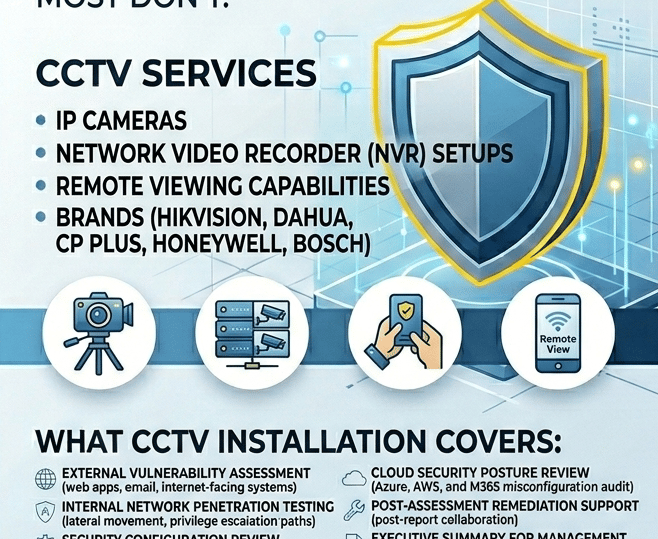
CCTV & Video Surveillance
A CCTV system is only useful if it covers the right places. Most don't.
IP Cameras · NVR · Remote Viewing · Hikvision · Dahua · CP Plus · Honeywell · Bosch
What CCTV installation covers:
Site survey and camera placement planning — coverage mapping before installation
IP camera installation — indoor dome, outdoor bullet, PTZ for large areas
Network Video Recorder (NVR) setup and storage configuration
Camera tamper and signal loss alerting
Storage planning — local NVR, NAS backup, and cloud storage options
Integration with access control systems — camera triggers on access events
Footage retention policy setup — 30, 60, or 90-day retention depending on requirement
Footage retrieval and export support for incident investigation
Ongoing maintenance contract and system health monitoring
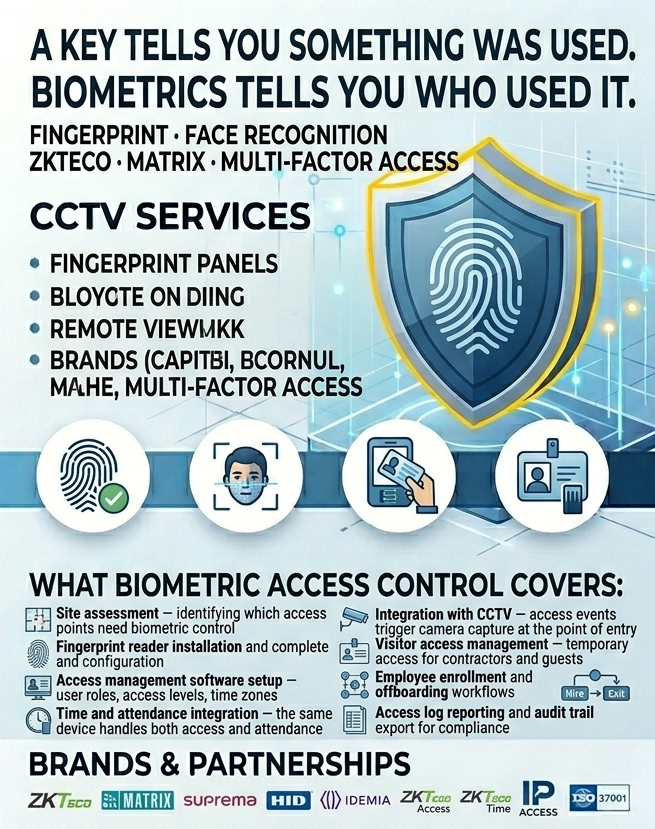
Biometric Access Control
A key tells you something was used. Biometrics tells you who used it.
Fingerprint · Face Recognition · ZKTeco · Matrix · Multi-factor Access
What biometric access control covers:
Site assessment — identifying which access points need biometric control
Fingerprint reader installation and complete staff enrollment
Face recognition terminal installation and configuration
Access management software setup — user roles, access levels, time zones
Time and attendance integration — the same device handles both access and attendance
Integration with CCTV — access events trigger camera capture at the point of entry
Visitor access management — temporary access for contractors and guests
Employee enrollment and offboarding workflows
Access log reporting and audit trail export for compliance





Q: We're a small business. Do we need all five of these services? No. You need the ones that address the actual risks your business faces. A 20-person professional services firm probably needs network security hardening, email security, and a basic security audit as the starting point. A warehouse with expensive equipment and stock needs CCTV and access control as the priority. A healthcare clinic needs both physical security and IT security with compliance documentation. We assess what's genuinely relevant for your situation and tell you honestly what to prioritise — we're not trying to sell every service on the list to every client.
Q: We already have CCTV installed. Can you maintain or upgrade it? Yes. We take over maintenance of existing systems installed by other vendors, assess whether cameras are placed and configured effectively, and upgrade components where gaps exist. If you have older analogue cameras, we'll assess whether upgrading to IP cameras makes sense for your specific requirements and give you an honest answer on cost versus benefit.
Q: What's the difference between a security audit and a penetration test? A security audit is a review — we look at your systems, configurations, policies, and access controls and identify gaps. A penetration test goes further — we actively attempt to exploit the vulnerabilities we find, with your knowledge and consent, to demonstrate what a real attacker could actually do with them. Audits give you a picture of your posture. Penetration tests give you proof of impact. Many clients do both — audit first to get the full picture, penetration test on specific areas to validate the severity of the most critical gaps.
Q: We had a security incident recently. Can you help? Yes. Post-incident review is one of the more common reasons businesses first contact us. We assess what happened, close the gaps that allowed it, and put controls in place to detect and prevent the same type of incident from recurring. We don't approach it as finding blame — we approach it as finding what needs to change so the same thing can't happen the same way again.
Q: Can you handle both the IT/cyber side and the physical security (CCTV, biometrics) side? Yes — and this is specifically why clients come to us rather than using separate vendors for each. The gap between IT security and physical security is where problems appear. A CCTV system running on the same network as your business systems without proper segmentation. A biometric access device with default credentials. A server room with strong network security but a door that anyone can open. We assess and address both sides, which means there are no gaps created by two teams never talking to each other.
Q: How long does a CCTV or biometric installation take? For a single-site installation — one office, standard number of cameras and access points — typically one to two days depending on cabling requirements. Larger or multi-site installations are scoped in advance and we give you a clear timeline before we start. We also minimise disruption to your working day — most installation work at occupied offices is done outside business hours or over weekends where required.
Q: Do you work with government and high-security environments? Yes. We've delivered managed security services for the Consulate General of the UAE's Hyderabad office — an environment with strict requirements around access controls, documentation, audit trails, and change management procedures. We have direct experience working within those requirements and are comfortable referencing that engagement to demonstrate capability for similar high-security environments.